PerimeterMFA offers unlimited flexibiility in how you can bring your user community into the Multi-Factor security realm. Gone are the Big Bang implementations where your entire user base is forced to adopt the chosen MFA protection on day one.
While different groups of users can take different paths towards full MFA adoption, below in an Example of how you may want to leverage Evolutionary Enrollment to maximize security and minimize user friction with a thoughtful, phased approach.

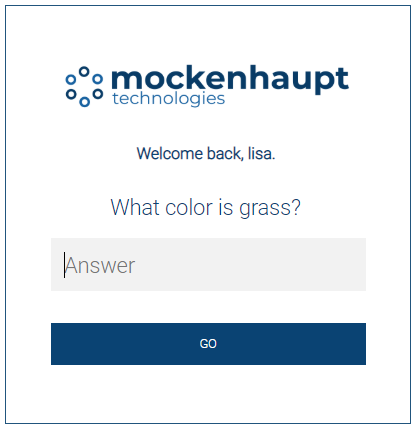 Not only do static questions protect against automated attacks, they can also be effective in acclimating your users
to a secondary challenge.
Not only do static questions protect against automated attacks, they can also be effective in acclimating your users
to a secondary challenge.
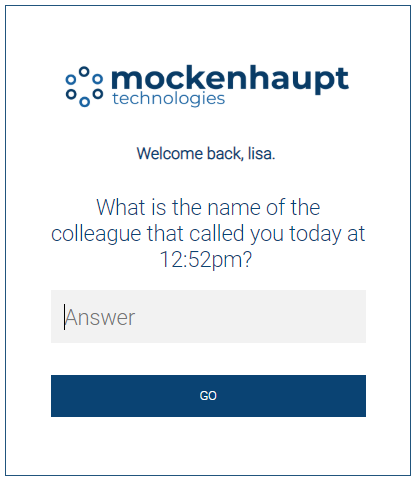 Dynamic questions offer a higher level of security than static questions and can be drawn from any internal data source, such as
Active Directory, Human Resource databases, Phone systems, Card Key systems or virtually any other data store.
Dynamic questions offer a higher level of security than static questions and can be drawn from any internal data source, such as
Active Directory, Human Resource databases, Phone systems, Card Key systems or virtually any other data store.
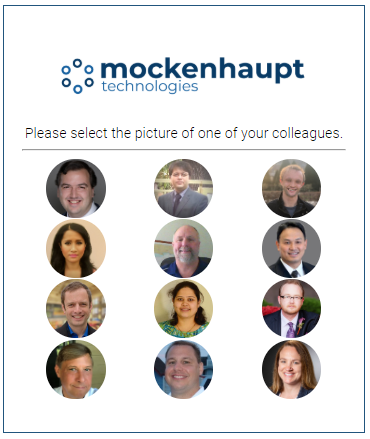 In this example, we are havesting 12 avatars from Active Directory - including the avatar of one of the requester's
colleagues.
In this example, we are havesting 12 avatars from Active Directory - including the avatar of one of the requester's
colleagues.